Fusion Role Based Security Model
 Oracle Fusion Applications use a role based access-control security model. Where users are assigned roles through which they gain access to functions and data within the applications. Unlike Oracle Ebiz user do not need to select different responsibilities once they log in, all roles are active concurrently i.e users do not have to select any role when they sign in.
Oracle Fusion Applications use a role based access-control security model. Where users are assigned roles through which they gain access to functions and data within the applications. Unlike Oracle Ebiz user do not need to select different responsibilities once they log in, all roles are active concurrently i.e users do not have to select any role when they sign in.
Role based security in Oracle Fusion Application controls WHO can do WHAT on WHICH data. For example: A line manager (who) can promote (what) an employee (which). This is also explained in the table below.
| Who | What | Which Data |
| Employee | Can see payslip | His own |
| Line Manager | Can Transfer/terminate | A worker from his team |
| HR | Can give promotion | Employees from a particular organization |
Understand with an example
 At the beginning it sounds confusing but once you get the basic its easier and convenient same as your responsibilities and functions in Ebiz. To understand it better lets put a hypothetical business requirement in-front of us.
At the beginning it sounds confusing but once you get the basic its easier and convenient same as your responsibilities and functions in Ebiz. To understand it better lets put a hypothetical business requirement in-front of us.
Now the function to terminate employee is already available with few seeded roles like Manager and HR Specialist but you can not assign them to Mr. Security as using the seeded role “Manager” he would be able to terminate only people falling under the manager hierarchy. You cannot also assign another seeded role “Hr Specialist” to Mr Security as it comes with many other powerful things along with Termination.
So the only option is to create a new custom role only for terminating employees and assign it to Mr Security. In the next steps we will see how can this be done.
Setup Steps
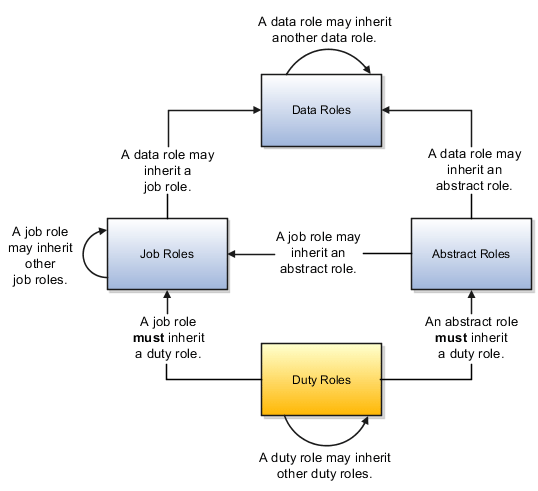
 Now we know that we have to create a new role but what would be the type of role as oracle fusion delivers four different types of role. So lets talk about different roles available in fusion before we login to application and start setting things up.
Now we know that we have to create a new role but what would be the type of role as oracle fusion delivers four different types of role. So lets talk about different roles available in fusion before we login to application and start setting things up.
Oracle Fusion Applications uses four types of roles for security management, which are given below. The first three roles can be assigned to user directly. These roles also inherit some or other roles.
Data Roles
Data roles are combination of worker’s job and the data instances on which jobs can be performed. For example, a data role Payroll Administrator Payroll US combines a job (Payroll Administrator) with a data instance (Payroll US). As job is the one factor it inherits Job Role and for the data, we attached a security profile with it (will be explained later)
Job Roles
Job role aligns with the job that a worker is hired to perform. Human Resource Analyst and Payroll Manager are examples of predefined job roles. Typically, you include job roles in data roles and assign those data roles to users. The IT Security Manager and Application Implementation Consultant job roles are exceptions, because they are not considered HCM job roles and do not restrict data using HCM security profiles.
Abstract Roles
Abstract roles represent a worker’s role in the enterprise, independently of the job that the worker is hired to do. There are three seeded abstract roles delivered with Oracle Fusion HCM. These are the Employee, Line Manager, and Contingent Worker roles. Abstract roles are assigned to user automatically when some event occurs like Hire an employee, Terminate an employee or Promote an employee.
Duty Roles
Data Role aligns with the individual duties that users perform as part of their job but not assigned to user directly. This role also grants access to work areas, dashboards, task flows, application pages, reports, batch programs, and so on. Duty roles are inherited by job and abstract roles, and can also be inherited by other duty roles. Needless to say we can create custom role also, if needed.
Below diagram shows how some of the role inherits other
Data Security Through Security Profiles
Before we start our setup steps there is one more important topic to discuss, Security Profiles. A security profile identifies a set of data of a single type, such as persons or organizations, for example : All workers in department HCM US. We can assign security profiles to:
- Data roles
- Abstract roles
- Job roles
We can create HCM security profiles for the following HCM business objects (can be changed with future releases)
- Person
- Organization
- Position
- Legislative Data Group
- Country
- Document Type
- Payroll
- Payroll Flow
Okay, enough theory, so by now we know that for our requirement we have to create a Data Role to assign user and that Data role should inherit a job role, which eventually inherit a duty role. We also need to create a security profile to restrict organization and attached with Data role. Here are the steps…
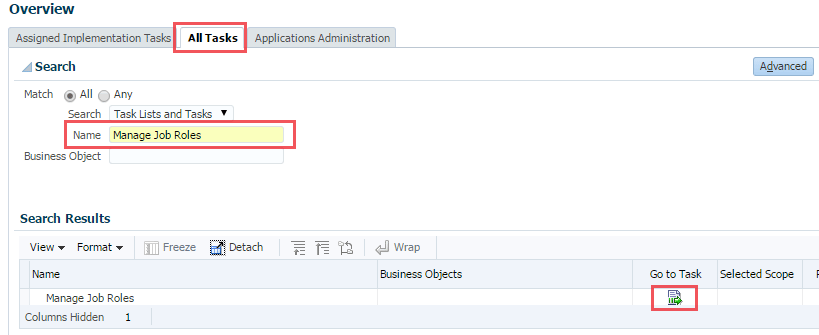
Step 01 : Create a Job Role
To create a job role search for the task “Manage Job Roles” and click on the Go to Task. This will open up a new window (OIM : Oracle Identity Manager)
Navigation : Navigator » Tools » Setup and Maintenance » All Tasks Tab » Search for Name Manage Job Roles
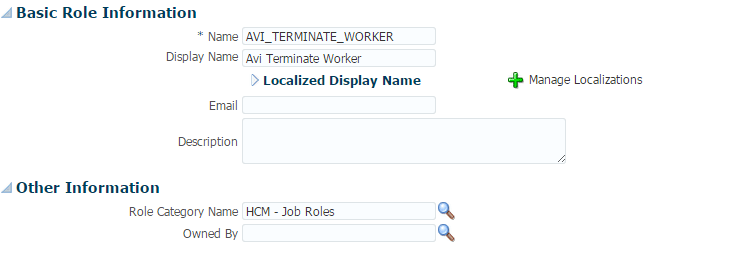
Click on the link Administration, top right corner. You will see a welcome page. Click on Create role (![]() ) under Roles. And enter details as given below. Once done click on save and close the window.
) under Roles. And enter details as given below. Once done click on save and close the window.
- Name : <Unique Name>
- Display Name : <Unique Display Name>
- Role Category Name : HCM – Job Roles
Step 02 : Map Duty role with Job role
From the above diagram and explanation we know that a Job Role must inherit a Duty Role. So to link a duty role with the job role we have created (Avi Terminate Worker), search for the task “Manage Duties” and click on Go to Task
Navigation : Navigator » Tools » Setup and Maintenance » All Tasks Tab » Search for Name Manage Duties
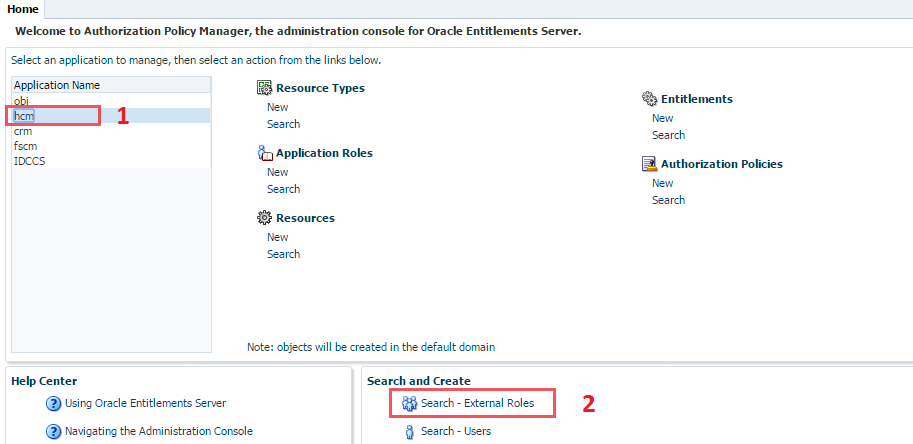
Once again this will open a new window (APM : Authorization Policy Manager). Click/select hcm from application name and then click on Search external Roles under search and create.
Note : All roles defined in the Oracle Identity Manager (OIM) are considered as External roles in Authorization Policy Manager (APM)
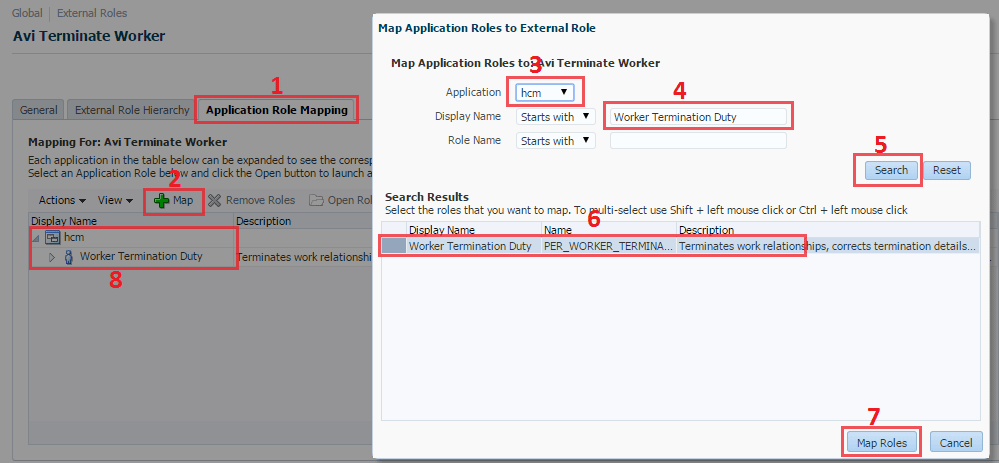
Now in the next page search for the role (Avi Terminate Worker) we created in OIM. In the search result section select the Job Role and click on “Open Role”. You will see following screen.
On the above page click on “Application Role Mapping” tab and click on +Map icon. It will bring a pop-up. Select hcm as application and search for the role “Worker Termination Duty” In the search reselct section click on the result and than click on Map Roles. Now we have successfully mapped the duty role with our job role. This duty role will help us to terminate the worker.
Step 03 : Run the process “Retrieve Latest LDAP Changes”
Navigation : Navigator » Tools » Scheduled Process
Now run the process “Retrieve Latest LDAP Changes”. We need to run this program to synchronize roles between LDAP and HCM. After successful run our job role will be available to HCM. Once the program status is succeeded we can move to next step.
Note : Please see the post Scheduling a Process in oracle Fusion to get an idea how process are schedules in Fusion application.
Step 04 : Create Security Profile (Optional)
Navigation : Navigator » Tools » Setup and Maintenance » All Tasks Tab »Search for Manage Person Security Profile
As we know we can attach security profile with Data role to give access on particular set of data. If you do not create any security profile you can select the “View All” option when creating Data role. In this example we will create a security profile based on Person Security profile.
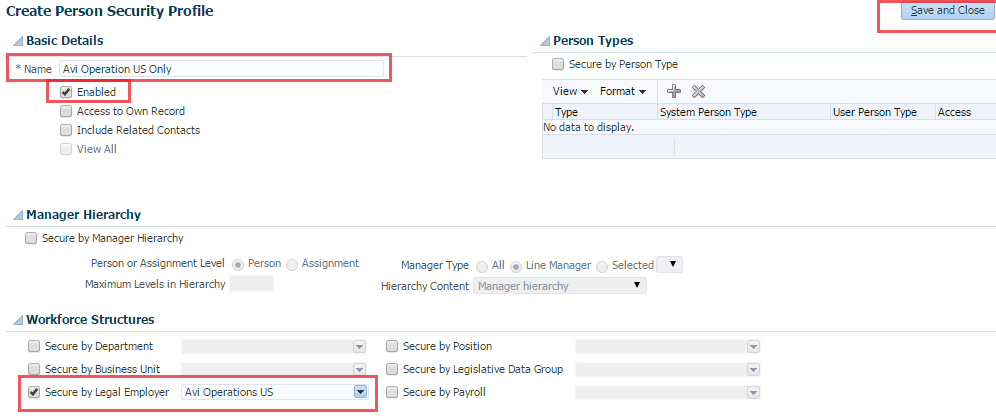
To create a security profile search for the task “Manage Person Security Profile” and click on Go to task icon. A new page will appear, in the search result section click on Create icon.
On the Create Person Security Profile page. Give it a name and select the check box Secure by Legal employer. From the list select the legal employer for which you want Mr Security to give access to terminate worker. Once done click on Save and close. Click Yes if when you receive warning.
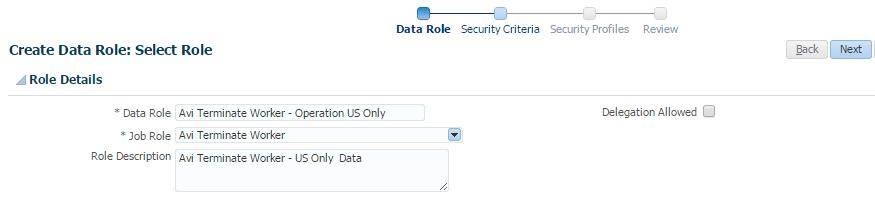
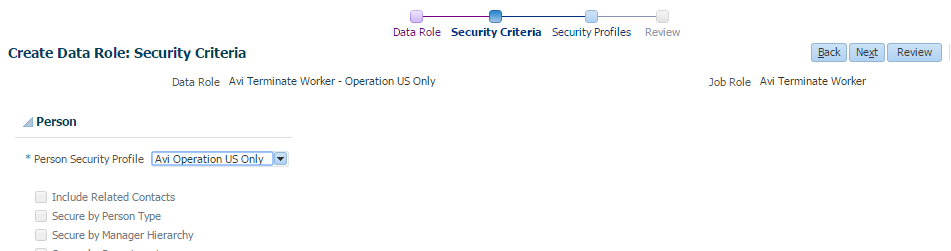
Step 04 : Create a Data Role
Navigation : Navigator » Tools » Setup and Maintenance » All Tasks Tab »Search for Assign Security Profiles to Role
Search for the task “Assign Security Profiles to Role” and click on Go to task. A new page will appear. In the search result section click on Create icon.
First give you data role a name and select the Job role that you create before. Once done click on Next.
In the next guided process select the security profile that you had created earlier. Once done click on Next
NOTE : If you did not follow the previous steps you can still create a security profile from here or just select the View All from the list.
Next screen will show all security profiles associated with this data role. Click on Next again, which will bring the Review Page. Review it once and once satisfied click on Submit.
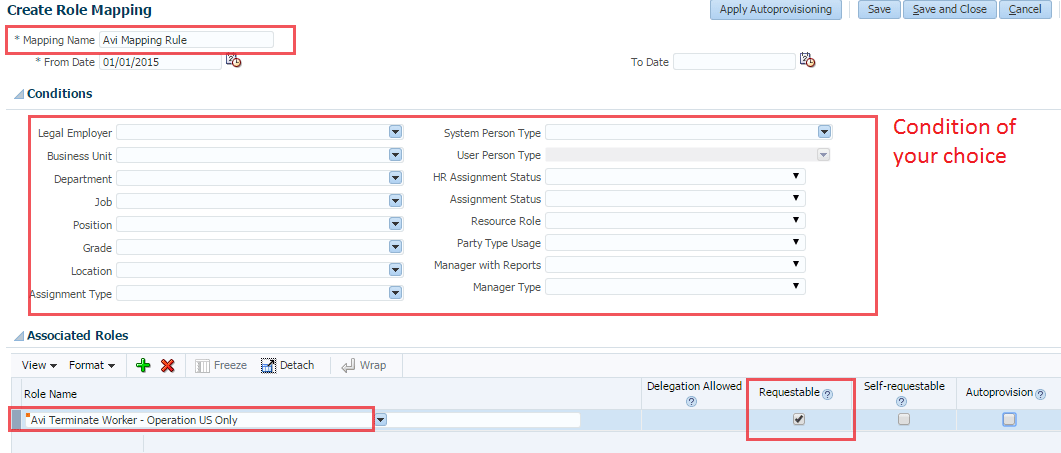
Step 06 : Create Role Provisioning Rule
Navigation : Navigator » Tools » Setup and Maintenance » All Tasks Tab » Search for Name Manage Role Provisioning Rules
Using the role provisioning rule we add an extra layer of security and can define which role will be available to which set of users. Using this we can also set rules to automatically assign a role to users if predefined conditions are met.
Search for the task “Manage Role Provisioning Rules” and click on Go to task. In the next page click on Create under the search result section. Give a mapping name, select Conditions (left blank in this example) and in the associated role section select the data role we have created. Please ensure requestable check box is selected and Autoprovision is unchecked. Click on Save and Close.
Note : If you notice “Delegation Allowed” option is disabled because when we created our data role (step 04) we did not select “Delegation Allowed” check box. We will discuss about role provisioning in details in some other topic.
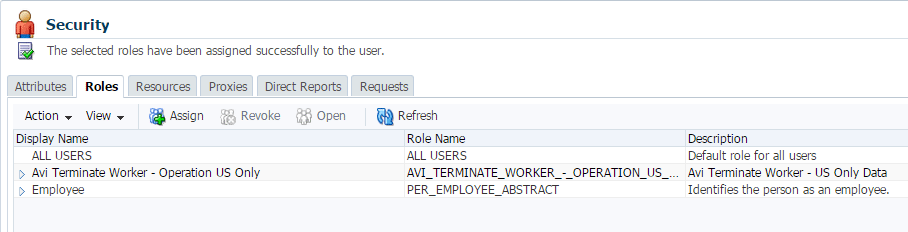
Step 07 : Assign Data Role to user
Now you Data role is ready. You can assign this to any person. There are different ways you can assign a role to user, either through OIM or from task “Manage Users”. We are assuming you are already aware aout this steps. In the below image Data Role was assigned through Oracle Identity Manager. You can see Mr. Security has two roles Employee (abstract Role) and Avi Terminate Worker – Operation US Only
Step 08 : Validate the Data Role Assigned to user
Navigation : Navigator » Person Gallery » Search for person
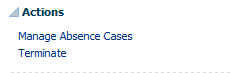 To validate the Data Role Mr. Security will login to application. Navigate to Person gallery and search for any worker. At left hand side under the Action menu he will see the option to terminate worker.
To validate the Data Role Mr. Security will login to application. Navigate to Person gallery and search for any worker. At left hand side under the Action menu he will see the option to terminate worker.
You can go through the post “Configure and Customize Approval Rules in Oracle Fusion” to see how an approval can be customized for termination.
Additional Resource for Fusion Role Based Security
I hope you will also like to check following oracle notes.
- Mapping Of Roles, Duties and Privileges in Fusion Applications (Doc ID 1460486.1)
- Mapping Of Duty Roles To Top Level Menu Entries in Fusion Applications (Doc ID 1459828.1)
Hope this article was of any help for you. You can let me know your thought by commenting in the comment section or/and by giving your review. You can also ask any question, if you have any, in our forum.











Hi Avinash,
Awesome article on the Security. Helped me a lot.
Thanks
Suyog
Thanks Suyog…
Happy to know it helped you… after all this website is to help each other.
Do recommend and share with your friends 🙂
Thanks
Avinash
Hi Avinash,
Is there a way in which we add/remove a duty for role and the changes can be seen immediately (or at least quickly) after logging in through the respective user. It is taking quite a long time for the changes to show up. Even if i have run the Retrieve LDAP changes process.
Thanks
Suyog
Strange,
It should come into effect as soon as program is completed successfully.
Is it happening all the time or for any specific role?
Thanks,
Avinash
Awesome Article, well done Avinash!